~12 min read | Published March 24, 2026
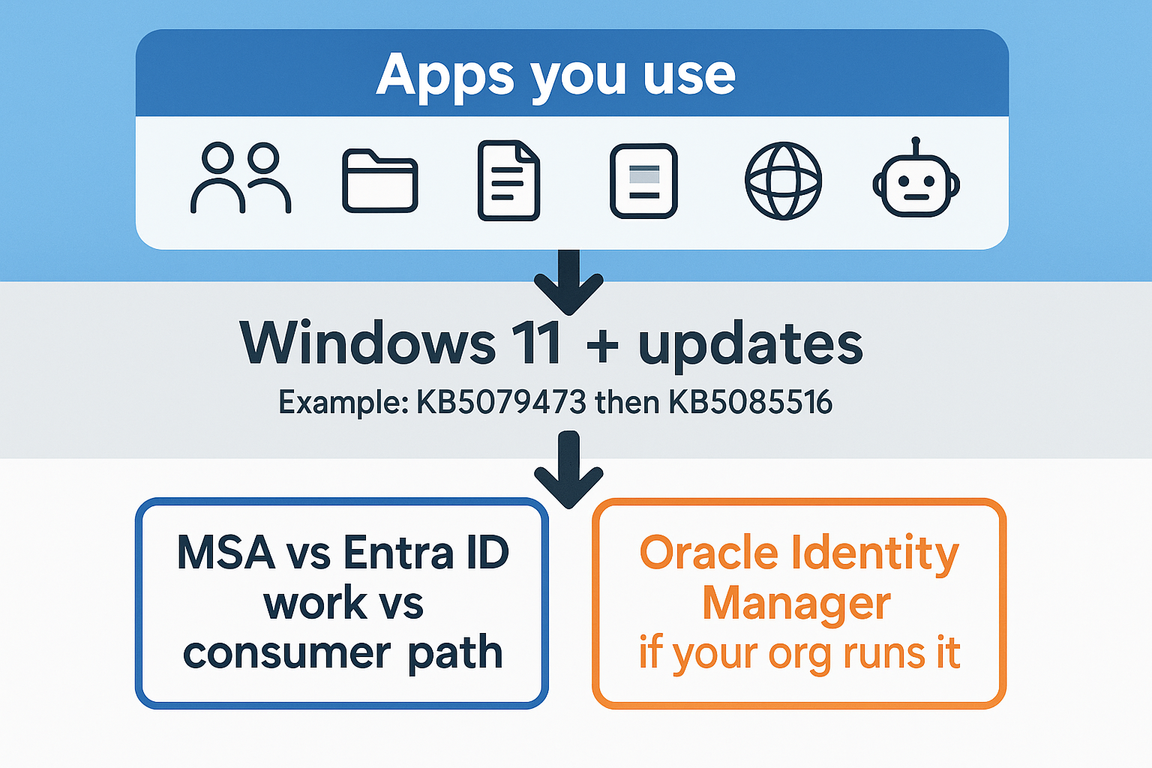
Quick answer: March 2026 included high-visibility emergency fixes on two different foundations. On Windows, a Patch Tuesday cumulative update led to Microsoft account sign-in failures for some apps, and Microsoft shipped an out-of-band fix (KB5085516). Separately, Oracle shipped out-of-band patches for a critical Identity Manager and Web Services Manager issue tracked as CVE-2026-21992.
Why this matters to you: If you build flows, support desktops, or own connectors that depend on Microsoft apps, the Windows item can look like a network outage when it is not. If your organization runs Oracle identity governance for provisioning, the Oracle item is about the system that creates and manages accounts.
For you if: You want plain English, clear scope, and sources you can forward to IT without embarrassment.
If you have ever watched someone reboot a machine three times because Teams insists the internet is down, you already know how much identity weirdness can waste a day. This month’s headlines are a good excuse to zoom out and remember what your day-to-day work sits on top of.
These patches are not the same class of issue, and your org might only care about one of them.
| Topic | What it is (plain English) | Typical signal at work |
|---|---|---|
| Windows / Microsoft apps KB5079473 regression, KB5085516 fix |
A March cumulative update could break Microsoft account sign-in for certain apps. Microsoft released an optional out-of-band update to address it. | Apps claim you are offline. Users blame WiFi. Help desk tickets spike. Microsoft 365 Copilot or Office features that rely on Microsoft account sign-in act broken. |
| Oracle identity products CVE-2026-21992 |
Oracle released emergency patches for a critical flaw in Identity Manager and Web Services Manager components. | Security forwards an Oracle alert. Identity governance or provisioning teams book an emergency change window. |

You can build the prettiest Power Automate flow in the world. If the machine cannot sign into the service layer, or if the identity system that provisions accounts is in trouble, your automation is usually not the first thing that breaks. The foundation is.
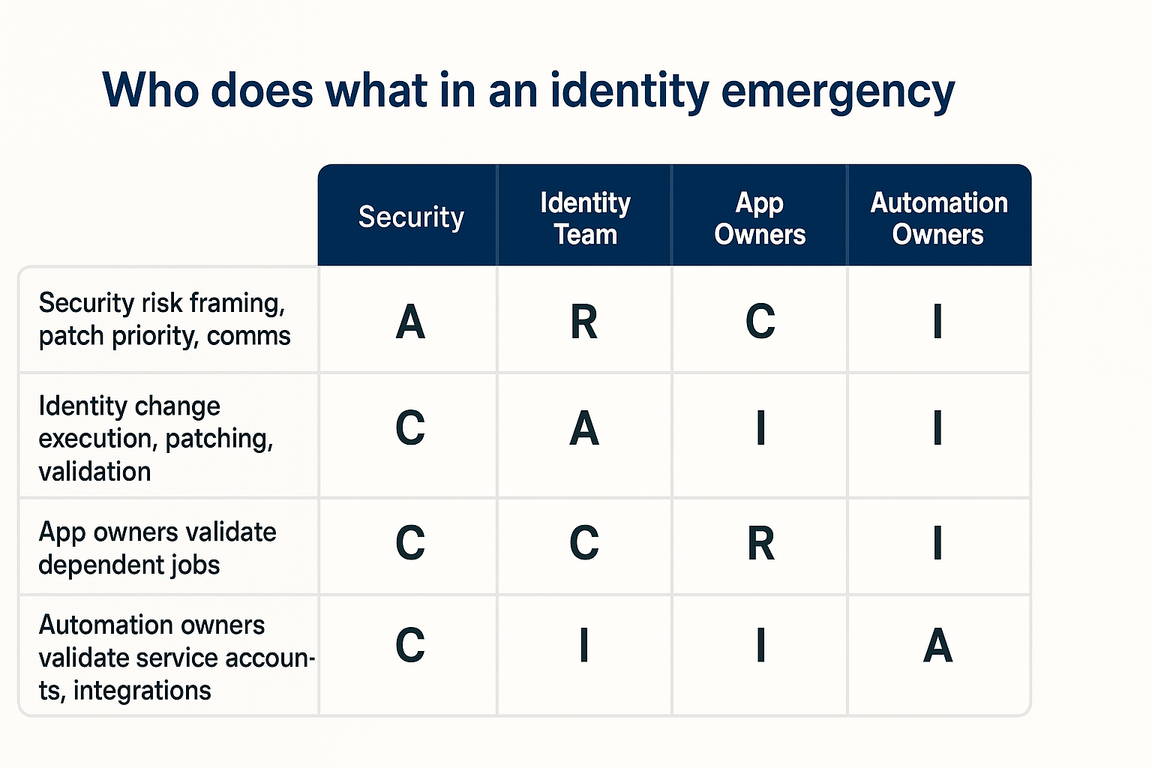
That is the practical reason to pair these stories under one umbrella. They are different vendors, different root causes, but the same lesson for people shipping work: know what your stack is authenticated as, and know which team owns the system underneath.
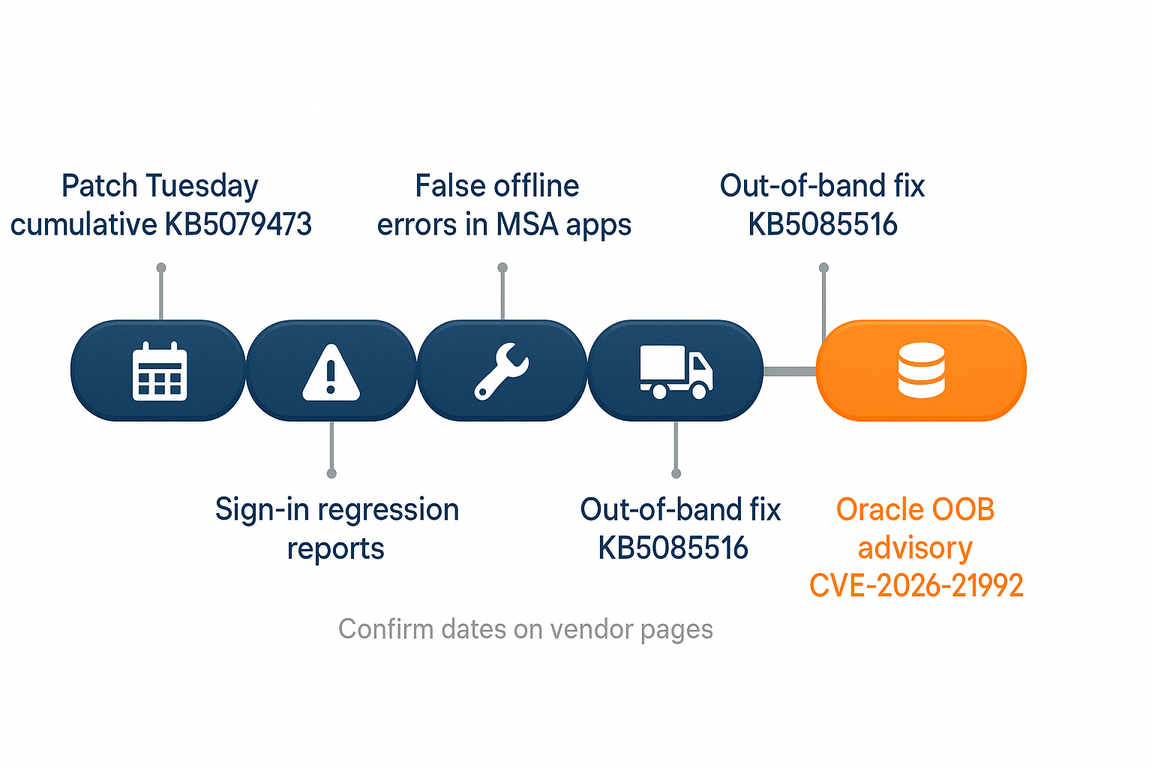
Coverage from BleepingComputer and Microsoft’s Windows release health pages describes the following sequence:
When the OS lies about connectivity, you can burn a morning chasing the wrong layer. Confirm basics, then confirm identity path and patch state.
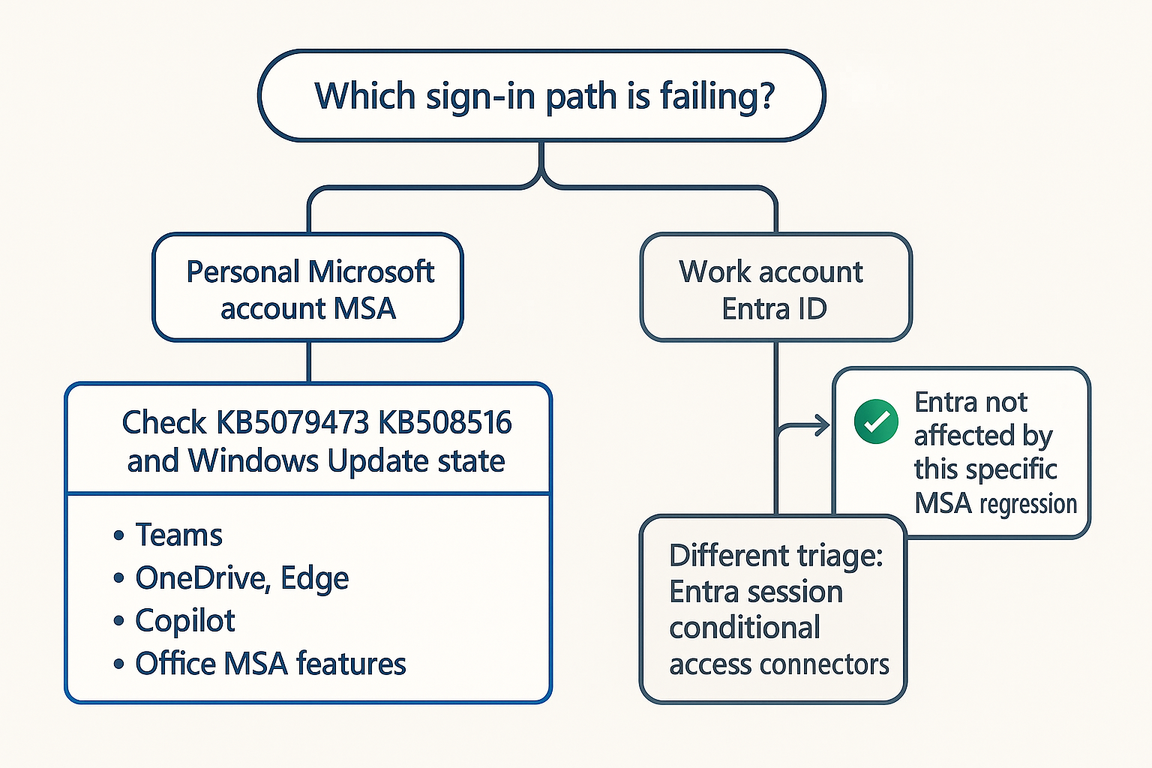
Microsoft account (MSA) is the consumer-style identity many people associate with a personal Microsoft login. Entra ID is Microsoft’s cloud identity for organizations, previously known as Azure Active Directory.
Microsoft’s public guidance, as summarized in independent reporting of the KB5079473 issue, states that the sign-in regression applies to operations involving Microsoft accounts and explicitly notes that businesses using Entra ID for app authentication would not be affected by this particular issue. If that sentence surprises your team, it is worth pausing. A lot of loud team chatter about Microsoft being down can be MSA-only, while work identity keeps moving.
For builders, the translation is simple. If your users primarily sign in with work accounts through Entra ID, do not let someone rewrite the whole story as a company-wide security meltdown until you confirm which identity path is actually failing.
Oracle shipped out-of-band updates for a critical issue tracked as CVE-2026-21992. Third-party reporting such as SecurityWeek summarizes Oracle’s advisory details:
Why you care in automation terms: Oracle Identity Manager is an enterprise identity governance tool used for user provisioning and access management across systems. If you do not run it, this is not your fire drill. If you do, this is the kind of patch that security and identity teams prioritize fast.
Reporting also notes a real-world uncertainty worth keeping straight: Oracle does not always state upfront whether a flaw has been exploited in the wild, and journalists have previously had to follow up after the fact. Translation for your leadership: treat the advisory as serious on its merits, follow your own patching discipline, and do not invent details the vendor has not published.
You can still use this as a teaching moment. Identity systems are high leverage. When they are wrong, everything downstream is wrong, including the service accounts and roles your integrations depend on.
You do not need a twelve-step framework. You need a short list your team can run this week.
Hot headlines sell fear. Your job is calmer than that. This Microsoft issue is mostly a story about a bad month for patch quality on a narrow identity path, and a vendor shipping a follow-on fix. It is annoying, costly, and real. It is also knowable.
The Oracle issue is a different kind of serious. It is the sort of item that belongs in security and identity runbooks, not in a rumor thread.
If you want one habit that pays off across both stories: when someone says authentication is broken, ask which identity store, which app surface, and which device patch level. Those three answers turn chaos into work.
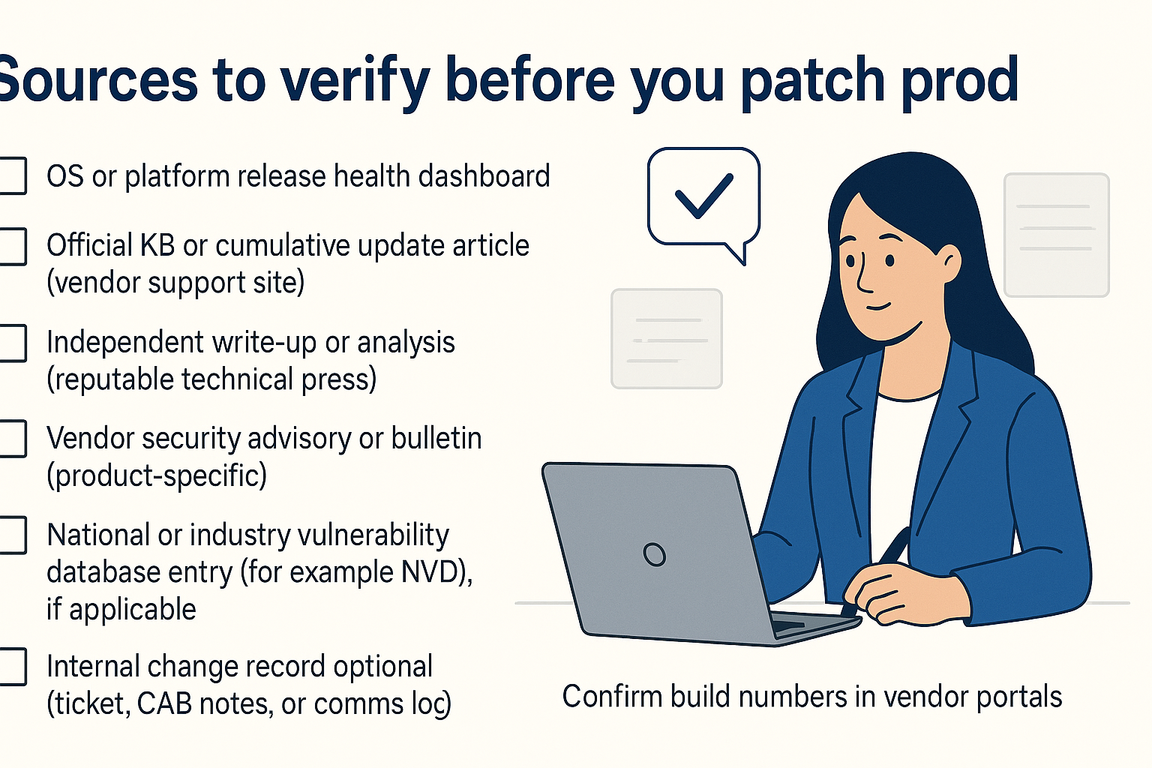
Microsoft released KB5085516 as an optional out-of-band update in March 2026 to address Microsoft account sign-in failures that could show up after KB5079473, including a false offline error. Start from Microsoft release health and the KB5085516 support article for the official wording on your channel.
Microsoft’s public description of this regression focused on Microsoft account sign-in paths, not Entra ID-based work sign-in for apps. If your failure is on work accounts through Entra ID, treat it as a different investigation path and verify before you broadcast a company-wide emergency.
No. It is an Oracle Fusion Middleware issue affecting Oracle Identity Manager and Oracle Web Services Manager. Windows admins might still get pulled in if downstream systems integrate, but the patch source is Oracle’s advisory and your identity team’s change process.
Quick Reference Kit from elijah.ai. This page summarizes publicly documented vendor and reputable press sources. It is not legal or security advice. Verify patch numbers, builds, and timelines against Microsoft and Oracle directly before you change production systems.